A quick tech note I want to jot down because it took me a LOT of Googling to find the answer.
Auto-patches in Github are clever!
I got an email from a GitHub bot while working today. It told me that there was an automatically-generated pull request waiting for me on a project I’ve not touched in a while that fixed a critical security vulnerability in a dependency – in this case the very popular “lodash” library.
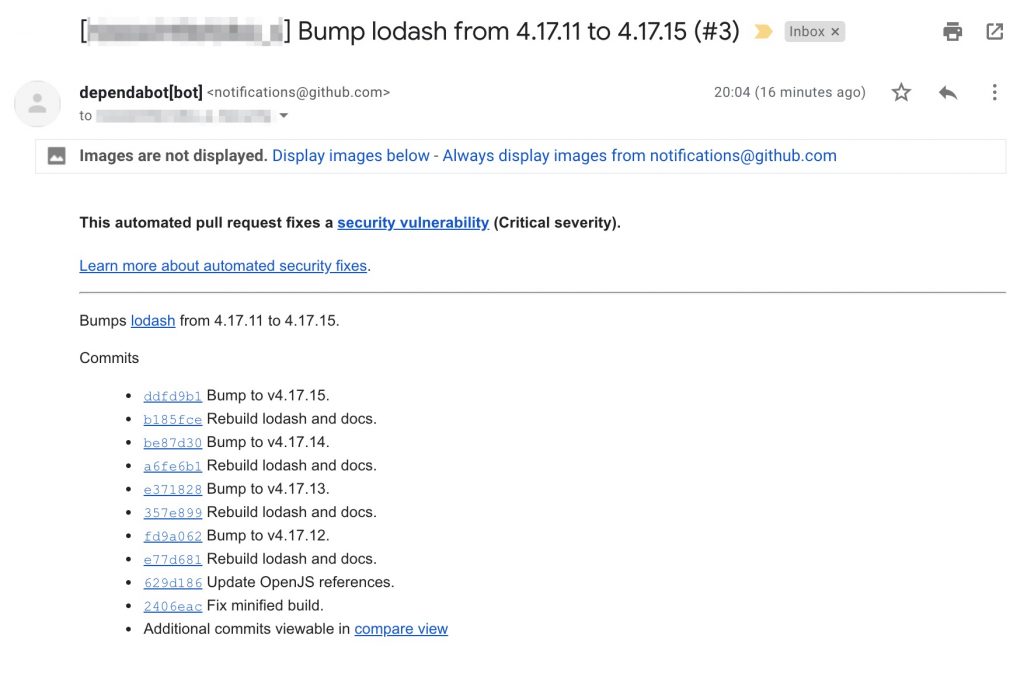
This is pretty neat! Thanks dependabot! (You can read more about automatic security updating in GitHub here)
But I trust nothing, especially computers. So I went looking at the pull request to see what it had done. Here’s the update to my package.lock file:
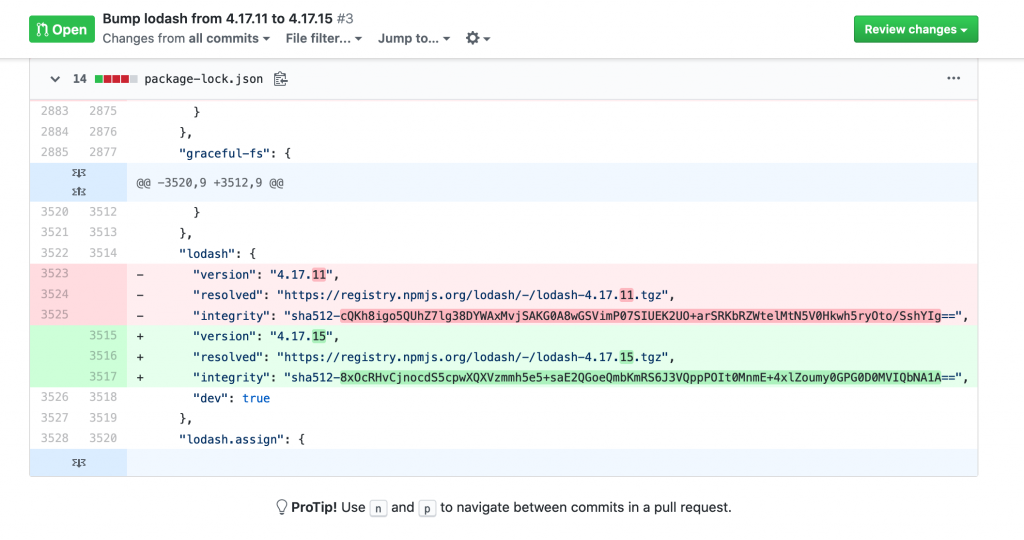
Just a simple minor version number bump and updated hash.
For those that don’t know, the hash is a special code that’s generated from all the files in the package. This code is always the same for the same set of files, and so I can test if the files I have are the same as the files that npm says I should have by generating the hash from my files and comparing it against the specified hash value.
If, for some reason, the hash of my files is different then I have different files and something might have been hacked and I should be very wary.
Anyway, the highly sensitive perfectionist in me wanted to know that dependabot had given me the right hash.
Finding the npm package’s hash
This article explains the process. But basically you go to:
https://registry.npmjs.org/[npm package name]
This gives you back some JSON. In Chrome I have an extension that pretty-prints JSON, but this is in Firefox which I think has JSON formatting built in.
You need to follow the JSON path through:
version- the version you want the hash for
dist
Then you will see the integrity value. This is the hash!
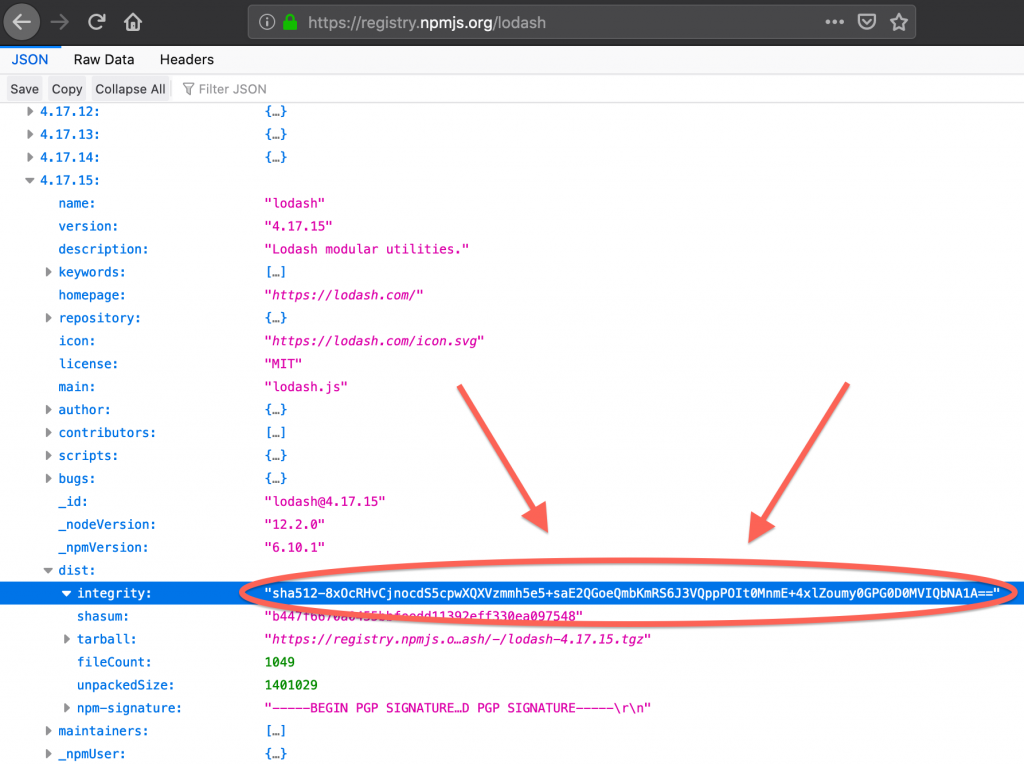
I can compare this value to the one in the pull request and be assured that, actually, I can trust the bot this time.
But will I next time?!